

Following design, implementation and validation testing of defensive network architectures and security countermeasures, an IACSIndustrial Automation and Control Systems and its associated security countermeasures will require to be maintained over its operational life.
Unlike the process and safety equipment it interfaces with, which tend to have a relatively stable risk profile throughout their life, IACS assets and associated security countermeasures are subject to a constantly evolving range of threats. Anorganisation’s cyber security programme should, therefore, be planned to mature over time, given sufficient skills and resources, to move from a reactive to a proactive state:

Increasing cyber security maturity and capability stages.
It is essential to maintain the Cyber Security Management System (CSMS) throughout the operate and maintain phase of the IACS assets and associated security countermeasures to ensure the policies and procedures remain relevant in light of operational experience, current vulnerability information and threat intelligence and any changes to your organisation’s regulatory framework.
Keep in mind that, unlike IT assets, maintaining security by patching vulnerabilities is not always an option for IACS assets. Where a patch is available but cannot be deployed e.g. if production downtime is not acceptable, if the patch is incompatible with an organisations IACS hardware, not approved by the IACS vendor or found to have an adverse effect on the IACS during testing, additional mitigation measures may need to be put in place. The US DHSUS Department of Homeland Security patch urgency decision tree is a useful tool for organisations having to balance security and operational risk decisions:
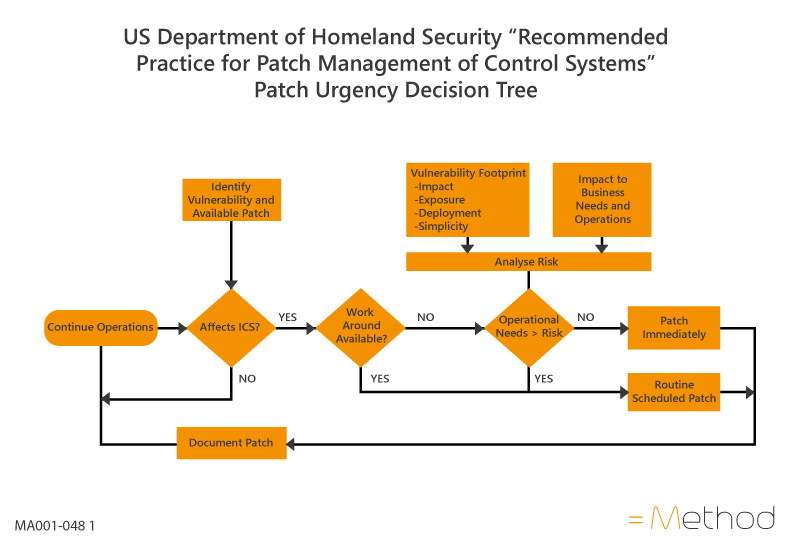
US Department of Homeland Security “Recommended Practice for Patch Management of Control Systems” Patch Urgency Decision Tree [see cisa.gov].
Staff training should be developed at an early stage in the implementation of a cyber security programme with refresher training given periodically (not more than 12 monthly) to aid development of a strong security culture within an organisation and maintain a current awareness of the requirements of the CSMS as well as security risks and countermeasures.
General cyber and physical security awareness training should be rolled out to all staff who interact with IACS assets e.g. Operations, Engineering, Maintenance staff as a means of improving basic cyber hygiene, reducing human error and improving detection of insider attacks.
Enhanced, role-specific training must be provided to personnel with defined responsibilities for IACS operations, maintenance and incident response under the CSMS.
Incident responseIncident response plans need to be intelligence-driven and tailored to the specific vulnerabilities of an industry or organisation’s IACS and must be supported by the architecture choices, threat detection capability and data logging methods chosen during IACS security design or improvement projects. Organisations should also develop consequence-based response plans for the most significant safety, environmental or business outcomes identified during risk assessment, irrespective of real-world evidence of such attacks occurring. The incident response plan should be based on:Maintaining safe operation; Minimising impact to operations; Maintaining availability of systems while under attack; Facilitating root cause analysis. Incident response plans are of little use if they are not exercised regularly, with representation from all responsible business functions (e.g. Operations, Engineering, Senior Management, Regulatory Compliance, Human Resources, Legal). Tabletop incident response exercises will allow each responsible department / person to understand how the organisation should act in response to a given incident, what information will be required to inform those actions, how quickly and easily that information can be made available and what communication or reporting structure will be necessary to respond to the incident effectively. and recovery plans should also be periodically reviewed, updated through a Change Management process and exercised regularly to enhance staff training and security preparedness.
You can contact =Method below:
p: +44 (0)1462 713313
E: support@methodcysec.com. T: 44 (0)1462 713313. W: www.methodcysec.com